Quantum Telecommunications Italy (QTI) is the first Italian quantum communications company to develop and produce Quantum Key Distribution systems. Telsy – the cybersecurity and cryptography competence centre of the TIM Group – has just become a QTI shareholder aiming to leverage the disruptive opportunities provided by quantum technologies.
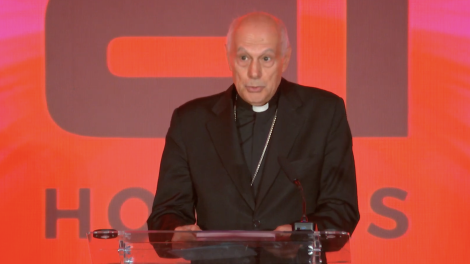
This association is geared towards producing a fully end-to-end encryption system compatible with current telecommunication infrastructure for private, governmental, and military applications. Decode39 reached out to Eugenio Santagata, CEO at Telsy and Chief Public Affairs & Security Officer at TIM, to understand the nature and importance of TIM Group’s latest investment.
The underwater world represents the future of humanity, as Admiral Enrico Credendino, Navy Chief of Staff, said recently. Will the new quantum technologies work in this domain?
Yes. Today, it is possible to generate quantum keys even underwater. In this case, we speak of Quantum Key Distribution (QKD) in free space, a type of technology also being developed in satellite applications; it’s an exciting area if we consider possible long-distance applications. Moreover, in the future, we will be able to implement QKD in transoceanic underwater fibre optics, where the TIM Group is already involved through Sparkle and its extensive undersea backbone.
Medical data protection, too, is among the potential applications. How important is it to ensure security in that field?
Medical data are sensitive by definition, as they belong to the personal sphere. That’s precisely why implementing QKD protocols is extremely important within the healthcare industry. It’s crucial to ensure high levels of security while exchanging patients’ clinical information between hospitals, diagnostic centres, laboratories, etc. A concrete example is remote surgery, where the physician has to manage hyper-sensitive and complex instruments and where it is essential to grant total security of the information exchanged between the equipment in use. Also, raising the IT security level in this area makes it possible to prevent illicit purchasing and data exchange activities on the dark web – which, unfortunately, is a pervasive phenomenon…
Telsy has focussed on Europe when building its supply chain. What does that mean in terms of security?
Telsy – a TIM Group company operating under TIM Enterprise – has a stake in QTI, a startup company active in quantum communications over fibre optics and innovative technologies based on national security standards. The market must have certainty about the technologies’ origin and the reliability of the expertise behind their development. Growing cybersecurity awareness is and will be instrumental in ensuring a robust National Cybersecurity Perimeter (the State’s cyber defence infrastructure for strategic assets, ed).
Telsy, as a company, for its part, is entirely made in Italy. It offers solutions developed by experts in the field and relies on the network infrastructure of TIM, Italy’s leading telco. Today, European technological independence is increasingly central – which prompts us to promote the development of a European digital industry.
In an ever-changing world, how long can QKD remain secure?
Forever, I would say. Today there is a lot of talk about quantum computing, supercomputers, speed, and incredible computing capabilities. Few know the consequences this can have on traditional encryption keys: much of it is inevitably bound to change. QKD makes it possible to cope with both the current threats (such as classical cyber attacks) and future threats (brought by, for example, quantum computers).
This tech also provides defence against the so-called “store and decrypt later” threats, where threat actors aim to exfiltrate data and information – even if momentarily inaccessible because it is protected by solid cryptography – and then decrypt them through new and emerging technologies, such as quantum computers.
QKD enables potentially unconditional security precisely because it rests on the inviolable and immutable laws of quantum mechanics: it does not use complicated mathematical algorithms to encrypt a message but exploits the physical properties of photons to exchange symmetric encryption keys between the communicating parties. And precisely because of the physical characteristics of photons, which are extremely sensitive to the slightest perturbations in the system, any eavesdropper can be revealed.